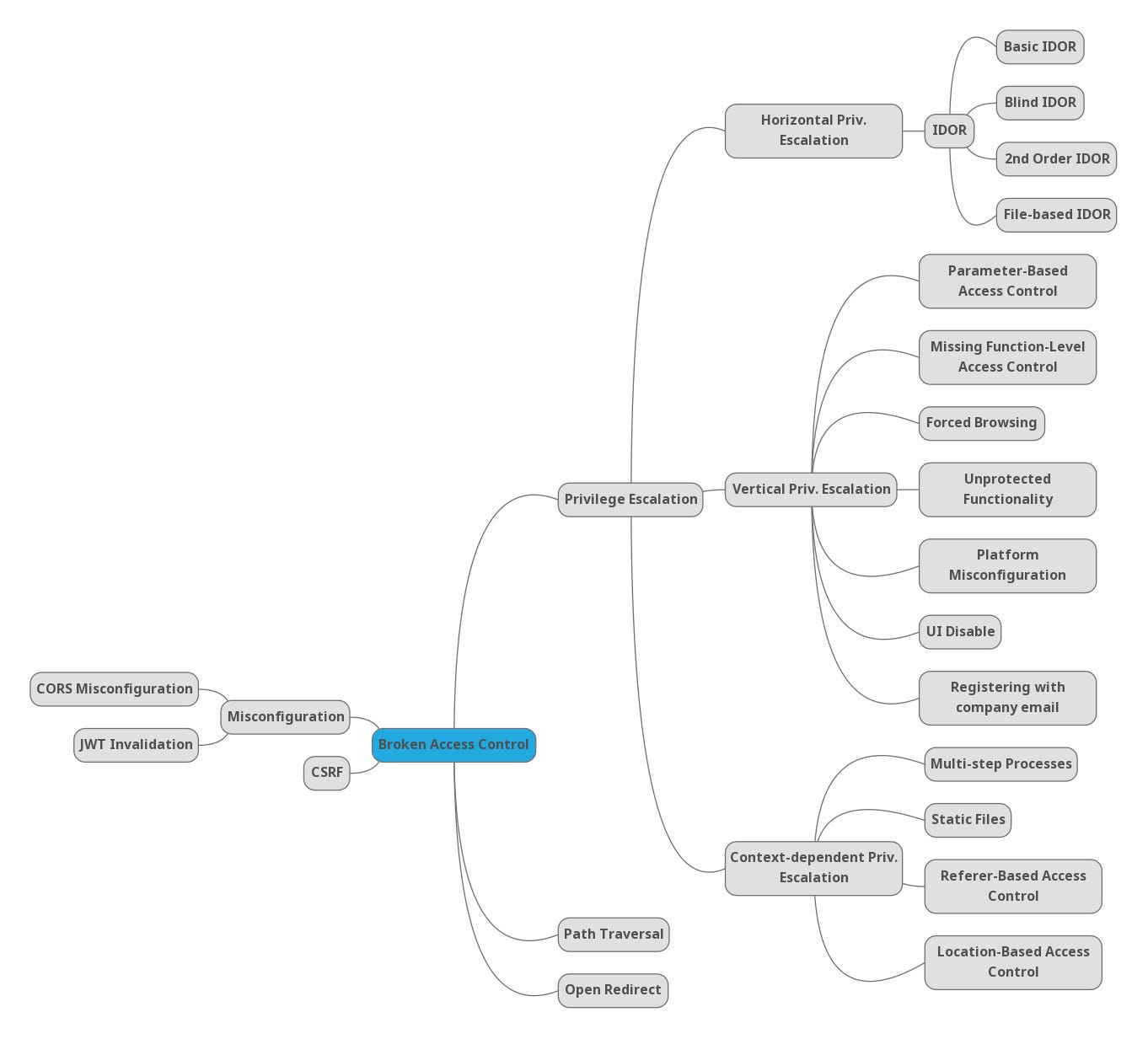
Rise of Broken Access Control. Why authorization flaws are trendy and… | by Rafin Rahman Chy | Nov, 2023 | InfoSec Write-ups

Manas on X: "Wanted to post this earlier. Always look for every possible way to find a broken access control, either endpoints or functionalities. Found 3 IDORS here. Reporting was average. @SynackRedTeam